By Eric D. Lawrence, DETROIT FREE PRESS
Kevin Tierney said he has been talking to officials at various universities for at least a decade about the issue of cybersecurity and the need to develop talent to tackle it.
Tierney has a key reason for his concern. As the chief cybersecurity officer for General Motors, he needs to ensure security across the GM ecosystem, which includes everything from the automaker’s vehicles to GM Financial to its Cruise subsidiary that’s focused on developing autonomous vehicles.
“I spend a lot of time ensuring we have the right talent,” Tierney said, noting that the high demand for cybersecurity expertise means jobs in the field are plentiful.
For the University of Detroit Mercy, that demand provided an opening for a new program.
“I’ve been talking to universities for 10 years plus on this topic and in the course of 2, 2½ years or so they stood up a program and are processing students … and some of those other schools I talked to 10 years ago maybe haven’t got to that level. They’ve moved fast,” Tierney said, noting that it’s challenging finding faculty who can even teach these topics.
GM works with other universities, such as Purdue and Virginia Tech, on cybersecurity issues, too, but the UDM program is different because it specifically focuses on vehicles, Tierney said.
UDM, with an enrollment of about 5,000 students, offers a graduate certificate as well as a master of science degree in vehicle cyber engineering, and is the lead entity on the Metro-Detroit Regional Vehicle Cybersecurity Institute, funded by a $1.12 million Department of Defense award announced in 2021. And Tierney is part of an 18-member advisory board that includes his counterparts at Ford and Stellantis.
The cybersecurity institute is a consortium of academic entities focused on bolstering the cybersecurity workforce, enrolling more than 250 students so far from high school, colleges and universities and the military, and includes Macomb, Oakland and Washtenaw community colleges, as well as the University of Arizona, which provides research support. The University of Michigan and Henry Ford College are slated to join in the upcoming academic year, according to information supplied by UDM.
UDM has a physical cyber lab but also virtual hands-on experiences so courses can be offered online. Other schools in the consortium can feed into the graduate programs, according to Paul Spadafora, director of professional engineering programs at UDM, who said the interest level was high as he reached out to officials in the auto industry.
Spadafora, who has a lengthy resume in the auto industry, including at GM, where he was a vehicle chief engineer responsible for vehicle launches around the globe, said he was told “we have great electrical engineers that we have to teach cyber to or we have great cyber security personnel, but they’re not engineers. It would be fantastic if we had a program where we trained vehicle cyber engineers and that was the birth of this program.”
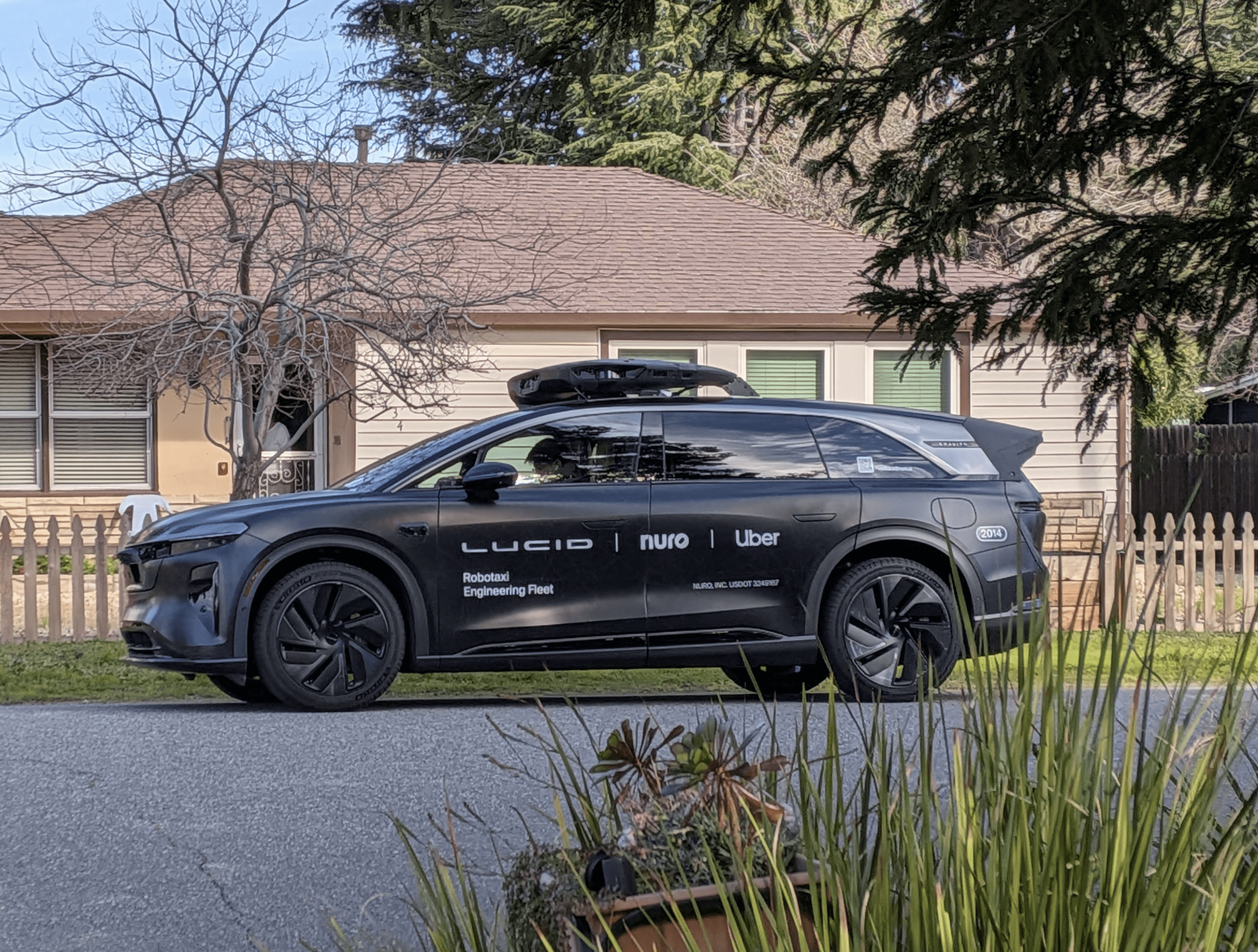
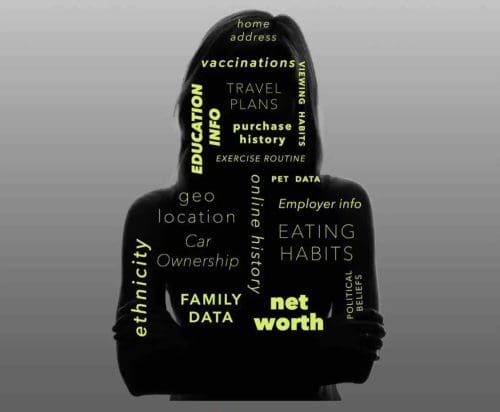
Spadafora described vehicle cybersecurity as a cat-and-mouse game. Automakers are focused on the issue and dedicating resources to the challenge, but the vulnerabilities continue to expand the more technologically advanced and connected vehicles become.
The potential vulnerabilities of automobiles to cyberattacks have been well-documented for years, perhaps most famously by the 2015 case of a Jeep Cherokee (opens in new tab). A writer for Wired described his trip as a guinea pig to showcase those vulnerabilities, driving “70 mph on the edge of downtown St. Louis” as hackers began toying with the vehicle’s climate control, radio and wipers before eventually cutting the transmission and leaving the SUV crawling in an area “with no shoulder to offer an escape.”
That case captured headlines, but the potential issues haven’t been limited to one make or model. A 2019 report from California-based Consumer Watchdog noted then that various automakers — Tesla, Daimler, Ford, GM, BMW and others — had disclosed cyber risks to their investors. That report called on automakers to install 50-cent “kill switches” (opens in new tab) so vehicles could be disconnected from the Internet and it raised the specter of a mass-casualty hacking event.
The UDM program and the consortium aim to create a pipeline to address the talent shortage.
“You need the students right now to be able to develop those systems that when fully electric, autonomous vehicles get here, they’re not able to be controlled,” Spadafora said.
But even before that transformation happens, the need for cybersecurity talent in the automotive industry is already evident and it becomes more key with the expansion of electric vehicles. Vehicle charging, for instance, potentially allows for a new entry point for hackers.
“Even today, even if the vehicle’s not autonomous, you could accelerate, steer, park, all electronically. In theory, if someone gets into your electrical architecture, they can take over your vehicle, so the need for security exists today,” Spadafora said.
And over-the-air updates, which are becoming more common in more vehicles, open vulnerabilities even as they allow for security updates.
Spadafora noted that cyber resiliency is a shared problem for both civilian transportation and the military.
“You can strip out the electronics, but the guts that go into an Army vehicle or a general product in the automotive industry (are) a shared issue, so if we solve for one, we solve for all,” he said, noting that although the military has additional “enablers” to make sure vehicles are secure “it’s a lot easier if you get an architecture that’s already cyber resilient.”
Katherine Snyder, dean of UDM’s College of Engineering and Science, said that meeting that challenge on the front end is one of the goals.
“You don’t want to be addressing cyber after the fact. And that’s why it’s so powerful to have cyber engineers who are designing for secure systems, rather than adding security after you’ve designed the system,” she said.
Although cybersecurity is needed across the economy, the automotive industry has specific challenges because of the relatively long development cycle and long product lifetime, said Tierney, the GM chief cybersecurity officer.
“We really have to try to think ahead, and we have to really see where’s the threat going and build as much of that into the vehicle now as we can. Because, of course, we can make some changes through the life of the vehicle to some extent, but a lot of it has to be baked in up front,” Tierney said.
Contact Eric D. Lawrence: [email protected] . Become a subscriber (opens in new tab).
This article originally appeared on Detroit Free Press: Vehicle cybersecurity gets boost from Defense Department (opens in new tab)